Large enterprise migration to post-quantum cryptography takes 12 to 15 years. That number comes from Campbell (2025), the most thorough empirical analysis of PQC migration timelines published to date (DOI: 10.3390/computers15010009). Fault-tolerant quantum computing — the kind that breaks today's encryption — is estimated to arrive between 2028 and 2033. If your organization started migrating today, you'd finish between 2038 and 2041. Five to eight years after the earliest threat window opens.
And almost nobody has started. PQC adoption across enterprises sits at 0.029%, according to Sowa et al. (2024). That's not a rounding error. That's an entire industry betting the house on "later."
Those numbers are uncomfortable. They're also navigable. You've closed gaps like this before — in cloud migration, in AI adoption, in every infrastructure transition where the cost of delay compounded quietly until it didn't. Not with alarm. With math, evidence, and a framework you can take to your board.
What You Need to Know This Week
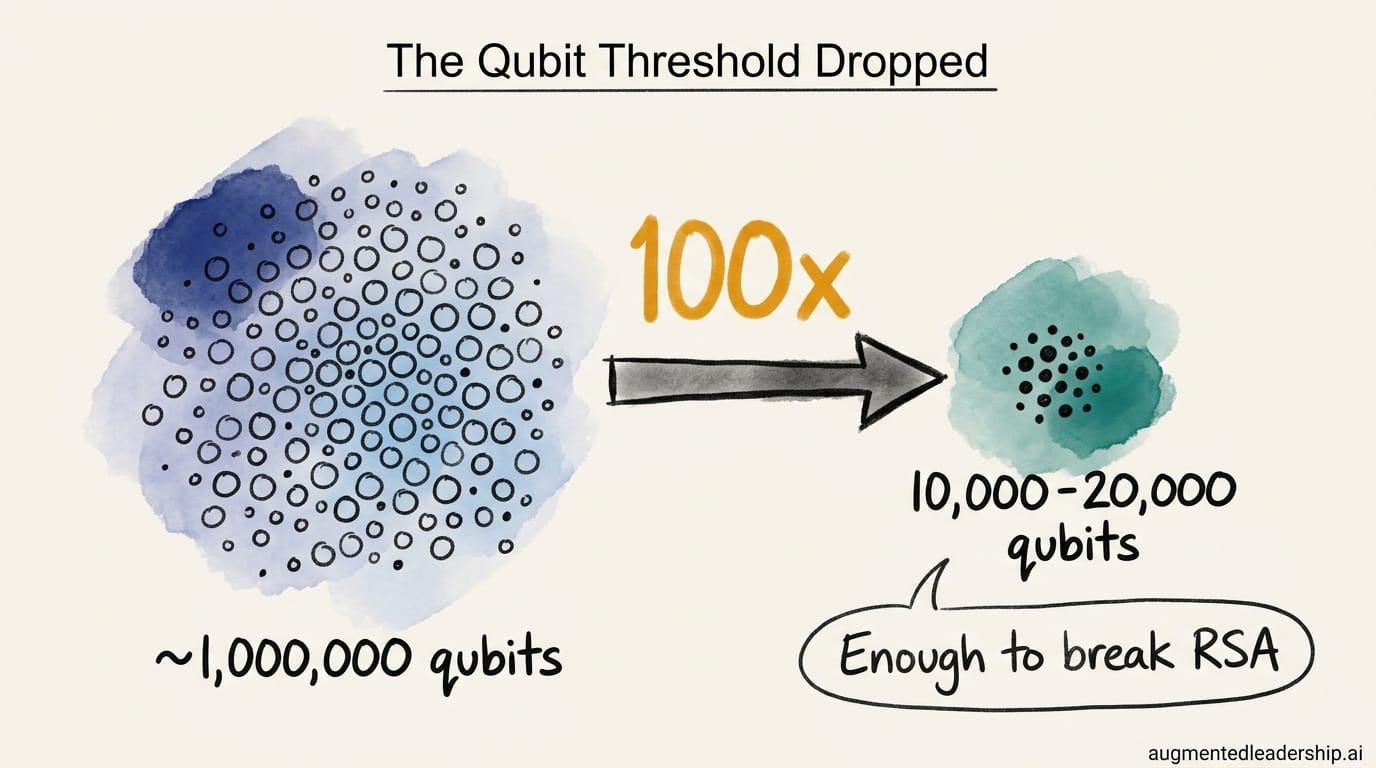
100x fewer qubits to break RSA. That's not a typo. Research from Caltech and Oratomic, in collaboration with Google (published April 7, 2026), demonstrated that RSA encryption could be broken with 10,000 to 20,000 qubits — down from prior estimates of roughly one million. Cloudflare responded by accelerating its PQC deadline to 2029. The assumption that "we have decades" rested on a hardware threshold that just dropped by two orders of magnitude. Whatever your internal timeline was, it was built on the old number.
Error correction crossed a critical threshold — twice. Quantinuum's Helios system hit 94 logical qubits from 98 physical qubits at 99.94% fidelity. IBM's Nighthawk processor delivered 120 qubits with a 10x improvement in error correction speed, a full year ahead of roadmap, fault-tolerant target now set for 2029. The "quantum can't stay coherent long enough" objection is losing its empirical footing.
Regulatory deadlines don't wait for quantum timelines. NIST FIPS 140-2 certificates deprecate on September 21, 2026 — five months from now. The Department of Homeland Security will not onboard new vendors without post-quantum encryption capability by end of 2026. PCI DSS v4.0 Requirement 12.3.3, active since March 2025, mandates annual cryptographic reviews for any organization processing payment data. Quantum is what makes these deadlines strategically urgent rather than routine. If you sell to the federal government or handle payments, this is a live compliance obligation.
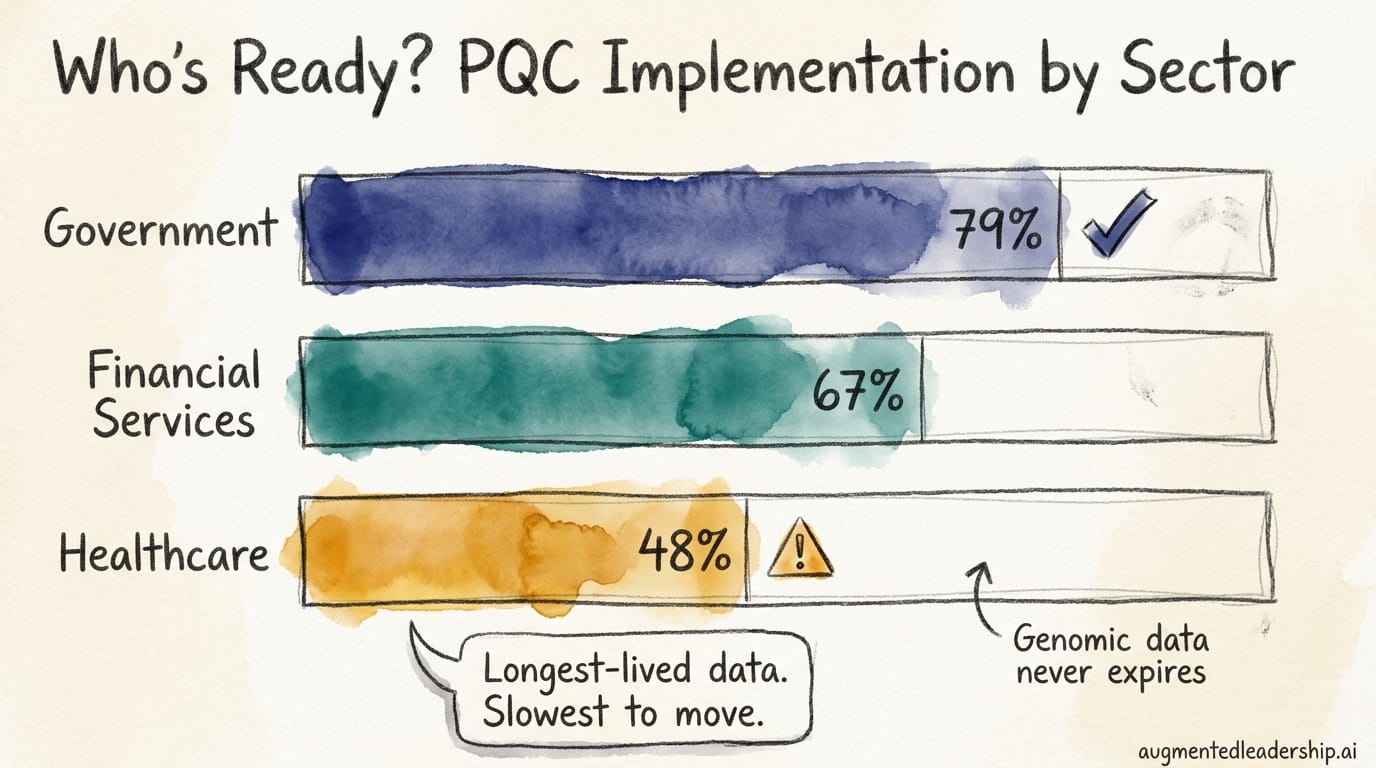
Where's healthcare? Government agencies report 79% PQC implementation. Financial services sits at 67% implementation. Healthcare — the sector with the longest-lived data and the most sensitive records — trails at 48% implementation. Patient records carry regulatory retention requirements measured in decades. Genomic data never expires. The industries with the most to lose from cryptographic exposure are moving the slowest. That's not a readiness gap. It's a liability gap.
The Readiness Gap Equation
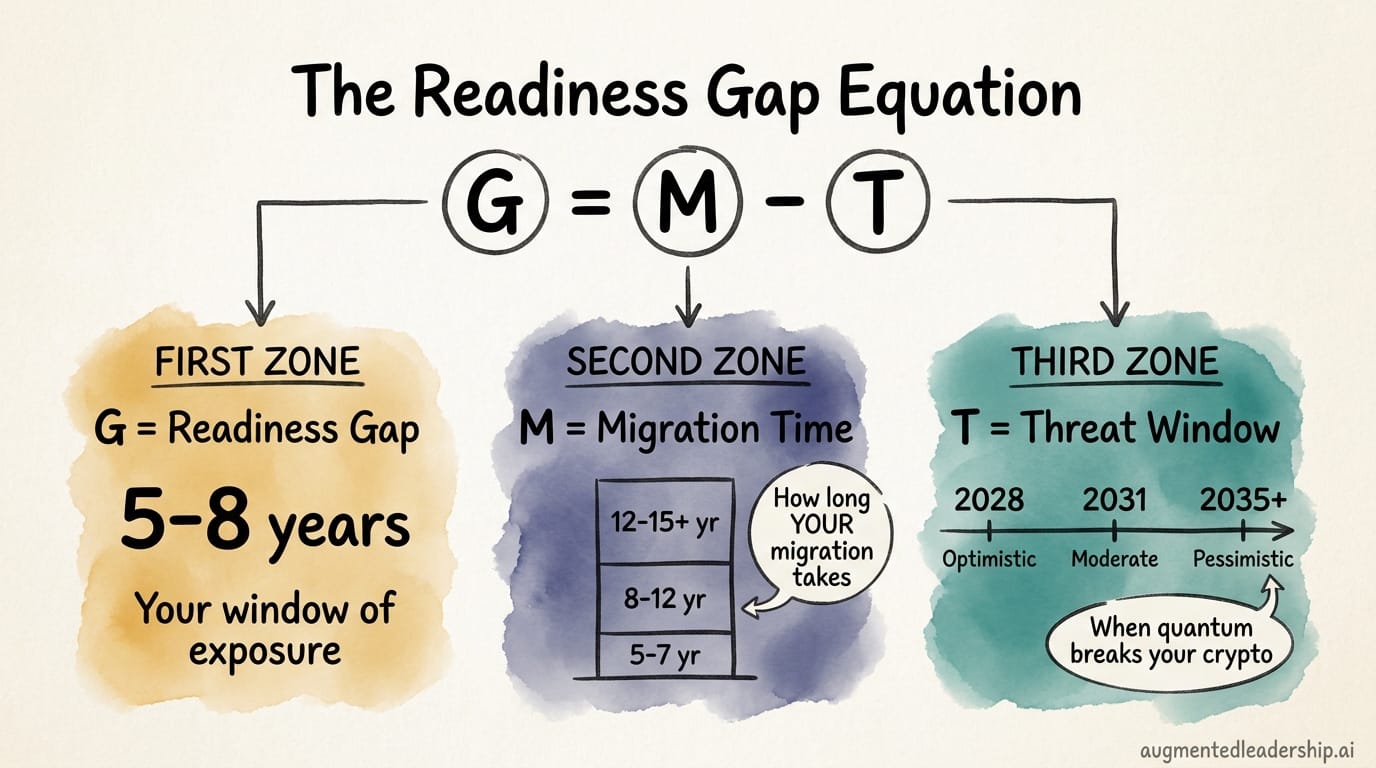
Your exposure comes down to three numbers.
Readiness Gap (G) = Migration Time (M) – Threat Window (T)
Migration Time (M) is how long full PQC migration will take your organization. Campbell (2025) provides empirical baselines: 5 to 7 years for small enterprises, 8 to 12 for mid-size, 12 to 15+ for large. These estimates assume you know what you're migrating. Most organizations have never inventoried their cryptographic estate — every certificate, key, protocol, and dependency across every system. Cryptography is embedded in layers most teams have never mapped: TLS configurations, database encryption, API authentication, firmware signing, third-party integrations. Without that inventory, M isn't a number. It's a guess.
A note on Campbell's figures: this is the best available empirical baseline, not ground truth. No one has completed a large enterprise PQC migration yet, and modern tooling may compress these timelines. But the organizations that prove these estimates wrong will be the ones that started early enough to learn what actually works.
Threat Window (T) is not a single date. It varies by data type. Long-lived data — medical records, financial archives, classified communications, intellectual property with multi-decade value — is already inside the threat window if harvest-now-decrypt-later (HNDL) attacks are economically rational. And they are: storage costs are trivially cheap, barriers to bulk interception are near zero, and the eventual decryption payoff is enormous. NIST, the Federal Reserve, and Europol all design their threat models against HNDL. As researcher Dolev Bluvstein, one of the paper's authors, noted, fault-tolerant quantum computing is "plausible, although not guaranteed, by end of the decade." Short-lived data — session tokens, ephemeral keys — has more runway. But your most valuable data likely doesn't.
Readiness Gap (G) is the result. For most large enterprises: G = 5 to 8 years of exposure. That's five to eight years during which your cryptographic infrastructure may be vulnerable and your migration is incomplete. The only way to shrink G is to reduce M.
Now calculate G under three scenarios. Optimistic T: 2028. Moderate T: 2031. Pessimistic T: 2035 or later. If G is positive under all three — and for any organization that hasn't started, it is — the case for action doesn't depend on which future shows up. This isn't a prediction model. It's a scenario-planning tool. The specific number matters less than the fact that it's positive in every reasonable case.
The counterargument is real and worth naming. Prediction markets remain skeptical that quantum advantage over classical encryption arrives before 2030. Prominent researchers including Gil Kalai and Scott Aaronson have questioned the pace of progress, though notably not the direction. Even the most skeptical voices in the field recommend migrating now. The debate is about speed, not destination — and that strengthens the case for starting immediately. Nobody credible is saying "don't migrate."
You cannot retrofit a building during an earthquake. Quantum migration is your cryptographic retrofit. The question is whether the foundation work is done before the ground shifts.
IBM's Quantum Readiness Index puts numbers on a familiar pattern. Fifty-nine percent of executives believe quantum-enabled AI will transform their industry by 2030. Only 27% expect their organization to be ready. That gap between belief and preparation — you've seen it before. The organizations that closed it early in cloud and AI transitions gained structural advantages that compounded for years.
The only variable you control is M. You need to know what you're migrating, someone needs to own it with real authority, and — this is the one most organizations miss — you have to stop making the problem bigger while you solve it. Every new system deployed without crypto agility extends your timeline. Complexity is a one-way ratchet unless someone is actively fighting it.
Your 90-Day Starting Position
If your organization is already implementing — and at 79% implementation in government and 67% in financial services, many are — then calculate G with your real numbers. If you haven't started, here is where to begin.
This month: Commission a cryptographic inventory. Tools like IBM Quantum Safe Explorer, CryptoNext COMPASS, and CipherScout can produce a Cryptographic Bill of Materials (CBOM) — a complete map of every cryptographic algorithm, protocol, certificate, and key in your environment. This is the single most important step because it converts M from a guess into a number. With FIPS 140-2 certificate deprecation five months out, federal suppliers can't afford to wait on this.
This quarter: Name an owner. Assign PQC migration to your CISO or CTO with explicit board risk committee reporting. Over half of organizations surveyed cite lack of executive support as the top barrier to migration progress. Ownership without authority is theater.
This quarter: Calculate your Readiness Gap. Brief your board with three numbers: your Migration Time (M), your Threat Window (T), and the resulting Gap (G). That single slide reframes quantum from an abstract technology risk to a measurable business exposure.
You don't need a quantum strategy yet. You need a starting position. And now you have one.

